Alteryx Designer Desktop Knowledge Base
Definitive answers from Designer Desktop experts.- Community
- :
- Community
- :
- Support
- :
- Knowledge
- :
- Designer Desktop
- :
- Licensing Error: Your computer is unable to access...
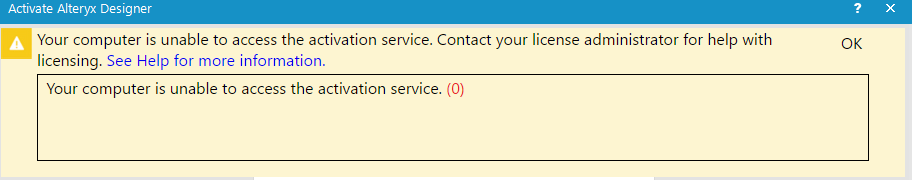
Licensing Error: Your computer is unable to access the activation service.
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Notify Moderator
03-16-2018 07:07 PM - edited 08-03-2021 11:26 AM
What does this error mean?
As we transitioned to a new licensing system in the 11.8 and 2018.1 releases, we changed how licenses are authenticated. The new licensing system relies on a few additionalsystem requirements, including a number of websites that are used during licensingand require access through your network firewall.
What's causing this?
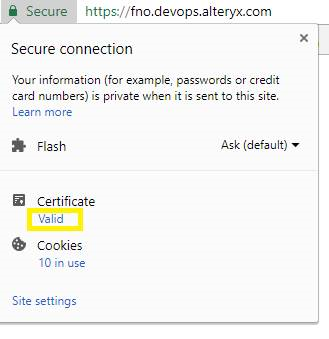
The new licensing system uses a TLS connection with fno.devops.alteryx.com, which is secured with an Amazon-issued TLS/SSL certificate.Alteryxis packaged with a copy of the Amazon certificate. The problem ariseswhen the network hasimplemented Deep Packet Inspection on TLS/SSL connections, which is a security measure requiring that a network device be able to intercept the connection and “see” the plaintext conversation. To do this, the device attempts to impersonate fno.devops.alteryx.combut uses its own certificate, which is separately installed as a trusted root certificate on the client computer. However, Alteryx doesn't consult the local computer's trust store when authenticating the license connection. Thus, when Alteryx attempts to construct a TLS session, it sees a certificate mismatch, and the connection fails.
The "quick-fix"
Since this is a network security restriction, you should have no problem activating if you move onto an external network such as a mobile hotspot, home network connection, or coffee shop.
Troubleshooting
How to confirm the problem
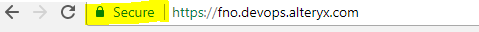
To definitively confirm that they are running into this issue, have them open a browser and go to https://fno.devops.alteryx.com.
It will show a blank screen, but up in the corner is certificate information. Click on the lock to view the certificate details.
This window needs to show this exact certification Path. If there are any extra or different entries, that's when this issue occurs.
How to fix it?
IT or your security department need to add a bypass on the SSL packet inspector such that https://fno.devops.alteryx.com is not subject to SSL deep packet inspection. After adding the bypass so this traffic is no longer being interdicted, the issue should be resolved and the customer should try to activate again.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
Thank you for sharing this.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
I'm having this exact issue, so I'm glad to have found this article.
It's unlikely that I can convince our IT department to make this change. Firewall / proxy are managed centrally, and we are a rather large company, so I doubt I can get this exception easily implemented -- my first challenge would be to find right person in IT who could address this issue and actually modify the rules.
From the description of the problem, may I ask why "the device ... impersonates fno.devops.alteryx.com" and "does not consult the local computer's trust store"? This seems to be contradictory with how certificate authentication is intended to work.
Yes, the "fix" is simple -- get out of the office to activate the Alteryx license. In my opinion, this "fix" is not an "enterprise" level solution.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
We had this exact problem, solution was to use the 'upload activation request' method for registering the tool. As we only have a few users this wasn't too painful, but agree not an enterprise option to register each time.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
Thanks for the feedback @brucedataguy and @戴卫!
I have a quick update about this issue:
Our development team has been working to resolve these issues, and as of Alteryx version 2018.1.4 (released early April) this is resolved for certificates that are not being passed through a proxy.
We're adding the proxy-support side of this to our upcoming 2018.2 release, so please stay tuned!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
Since we use proxy to connect to internet, 2018.1.4 did not solve the issue, so I'm looking forward to 2018.2 to avoid others who are likely to experience this activation error when upgrading from Version 11.7 (which is what happened to me).
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
I also now learned that my license key for 11.7 will not work for 2018.1.x, and a new key is to be issued to me for use when upgrading to 2018.1.x. So I am hitting multiple challenges in my scenario -- wrong key format (11.7 --> 2018.1.x) and proxy/deep packet inspection situation due to new license activation method starting with 11.8.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
Hi
I am trying to fix the same problem with Alteryx 2019.3.2.15763. We have a lot of licenses an it is impossible one by one.
Could you help me?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
In general, please see the documentation to Troubleshoot Activation Issues
Note: I have seen some cases where the command-line method of activation was successful after getting the "Your computer is unable to access the activation service." message.
AlteryxActivateLicenseKeyCmd.exe [license key] [email address]
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
I am receiving the same error for 2018.1.
I have a 2018.1 designer installed as admin, and a 2020.4 designer installed as non-admin. One day I attempted to start up the 2018.1 designer as an admin, but now I receive this error whenever I try to open either program.
Can you help me as well?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Notify Moderator
This error message indicates that the machine is having issues connecting to the Alteryx activation service. This is typically due to the firewall/proxy on the machine or could be because there is now a corporate firewall rule preventing access to the Alteryx license servers.
Please follow these instructions. You may have to contact your organization's IT department for assistance.
- Make sure that Port 80 or Port 443 is open.
- The System Requirements of the licensing system require access to whitelist.alteryx.com. Please make sure that your organization's network has not blocked communication to this endpoint.
- If your organization uses a proxy, be aware that the activation request packets are encrypted and might be being blocked.
Alternatively, you can do an offline activation with a license file. Follow the instructions at Activate License Offline.
If you are still having problems, please contact Alteryx Support.
-
2018.3
17 -
2018.4
13 -
2019.1
18 -
2019.2
7 -
2019.3
9 -
2019.4
13 -
2020.1
22 -
2020.2
30 -
2020.3
29 -
2020.4
35 -
2021.2
52 -
2021.3
25 -
2021.4
38 -
2022.1
33 -
Alteryx Designer
9 -
Alteryx Gallery
1 -
Alteryx Server
3 -
API
29 -
Apps
40 -
AWS
11 -
Computer Vision
6 -
Configuration
108 -
Connector
136 -
Connectors
1 -
Data Investigation
14 -
Database Connection
196 -
Date Time
30 -
Designer
204 -
Desktop Automation
22 -
Developer
72 -
Documentation
27 -
Dynamic Processing
31 -
Dynamics CRM
5 -
Error
267 -
Excel
52 -
Expression
40 -
FIPS Designer
1 -
FIPS Licensing
1 -
FIPS Supportability
1 -
FTP
4 -
Fuzzy Match
6 -
Gallery Data Connections
5 -
Google
20 -
In-DB
71 -
Input
185 -
Installation
55 -
Interface
25 -
Join
25 -
Licensing
22 -
Logs
4 -
Machine Learning
4 -
Macros
93 -
Oracle
38 -
Output
110 -
Parse
23 -
Power BI
16 -
Predictive
63 -
Preparation
59 -
Prescriptive
6 -
Python
68 -
R
39 -
RegEx
14 -
Reporting
53 -
Run Command
24 -
Salesforce
25 -
Setup & Installation
1 -
Sharepoint
17 -
Spatial
53 -
SQL
48 -
Tableau
25 -
Text Mining
2 -
Tips + Tricks
94 -
Transformation
15 -
Troubleshooting
3 -
Visualytics
1
- « Previous
- Next »